Map of the Stars
WHISTLEBLOWING - SURVEILLANCE, 15 Sep 2014
The NSA and GCHQ Campaign against German Satellite Companies
“Fuck!” That is the word that comes to the mind of Christian Steffen, the CEO of German satellite communications company Stellar PCS. He is looking at classified documents laying out the scope of something called Treasure Map, a top secret NSA program. Steffen’s firm provides internet access to remote portions of the globe via satellite, and what he is looking at tells him that the company, and some of its customers, have been penetrated by the U.S. National Security Agency and British spy agency GCHQ.
Stellar’s visibly shaken chief engineer, reviewing the same documents, shares his boss’ reaction. “The intelligence services could use this data to shut down the internet in entire African countries that are provided access via our satellite connections,” he says.
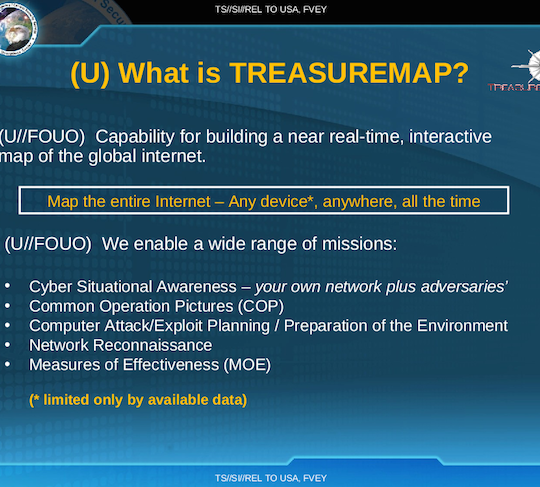
Treasure Map is a vast NSA campaign to map the global internet. The program doesn’t just seek to chart data flows in large traffic channels, such as telecommunications cables. Rather, it seeks to identify and locate every single device that is connected to the internet somewhere in the world—every smartphone, tablet, and computer—”anywhere, all the time,” according to NSA documents. Its internal logo depicts a skull superimposed onto a compass, the eyeholes glowing demonic red.
The breathtaking mission is described in a document from the archive of NSA whistleblower Edward Snowden provided to The Intercept and Der Spiegel. Treasure Map’s goal is to create an “interactive map of the global internet” in “almost real time.” Employees of the so-called “Five Eyes” intelligence alliance—England, Canada, Australia, and New Zealand—can install and use the program on their own computers. It evokes a kind of Google Earth for global data traffic, a bird’s eye view of the planet’s digital arteries.
The New York Times reported on the existence of Treasure Map last November. Though the NSA documents indicate that it can be used to monitor “adversaries,” and for “computer attack/exploit planning”—offering a kind of battlefield map for cyber warfare—they also clearly show that Treasure Map monitors traffic and devices inside the United States. Unnamed intelligence officials told the Times that the program didn’t have the capacity to monitor all internet-connected devices, and was focused on foreign networks, as well as the U.S. Defense Department’s own computer systems.
The Treasure Map graphics contained in the Snowden archive don’t just provide detailed views of global networks—they also note which carriers and internal service provider networks Five Eyes agencies claim to have already penetrated. In graphics generated by the program, some of the “autonomous systems”—basically, networks of routers all controlled by one company, referred to by the shorthand “AS”—under Treasure Map’s watchful eye are marked in red. An NSA legend explains what that means: “Within these AS, there are access points for technical monitoring.” In other words, they are under observation.
In one GCHQ document, an AS belonging to Stellar PCS is marked in red, as are networks that belong to two other German firms, Deutsche Telekom AG and Netcologne, which operates a fiber-optic network and provides telephone and internet services to 400,000 customers.
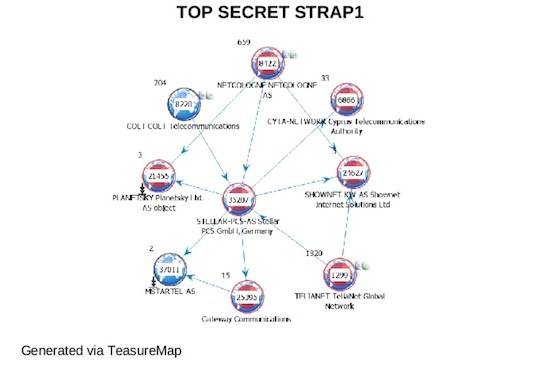
A Treasure Map image from a GCHQ document shows Stellar PCS and other companies marked red, meaning their networks have been penetrated
Deutsche Telekom, of which the German government owns more than 30 percent, is one of the dozen or so international telecommunications companies that operate global networks—so-called Tier 1 providers. In Germany alone, Deutsche Telekom claims to provide mobile phone services, internet, and land lines to 60 million customers.
It’s not clear from the documents how or where the NSA gained access to the networks. Deutsche Telekom’s autonomous system, marked in red, includes several thousand routers worldwide. It has operations in the U.S. and England, and is part of a consortium that operates the TAT14 transatlantic cable system, which stretches from England to the east coast of the U.S. “The accessing of our network by foreign intelligence agencies,” said a Telekom spokesperson, “would be completely unacceptable.”
The fact that Netcologne is a regional provider, with no international operations, would seem to indicate that the NSA or one of its partners accessed the network from within Germany. If so, that would be a violation of German law and potentially another NSA-related case for German prosecutors, who have been investigating the monitoring of Chancellor Angela Merkel’s mobile phone.
Reporters for Der Spiegel, working in collaboration with The Intercept, contacted both companies several weeks ago in order to give them an opportunity to look into the alleged security breaches themselves. The security departments of both firms say they launched intensive investigations, but failed to find any suspicious equipment or data streams leaving the network. The NSA declined to comment for this story, and GCHQ offered no response beyond its boilerplate claim that all its activities are lawful.
Deutsche Telekom and Netcologne are not the first German companies to be pinpointed by Snowden documents as having been successfully hacked by intelligence agencies. In March, Der Spiegel reported on a large-scale attack by GCHQ on German satellite operators Stellar, Cetel, and IABG, all of which offer satellite internet connections to remote regions of the world. All three companies operate their own autonomous systems. And all three are marked red in Treasure Map graphics.
Der Spiegel also contacted 11 of the international providers listed in the Treasure Map document. Four answered, all saying they examined their systems and were unable to find any irregularities. “We would be extremely concerned if a foreign government were to seek unauthorized access to our global networks and infrastructure,” said a spokesperson for the Australian telecommunications company Telstra.
The case of Stellar illustrates the lengths to which GCHG and NSA have gone in making their secret map of the internet, and its users.
One document, from GCHQ’s Network Analysis Center, lays out what appears to be an attack on Stellar. The document lists “central employees” at the company, and states that they should be identified and “tasked.” To “task” somebody, in signals intelligence jargon, is to engage in electronic surveillance. In addition to Stellar CEO Christian Steffen, nine other employees are named in the document.
The attack on Stellar has notable similarities with the GCHQ surveillance operation targeting the Belgian provider Belgacom, which Der Spiegel reported last year. There too, the GCHQ Network Analysis department penetrated deeply into the Belgacom network and that of its subsidiary BICS by hacking employee computers. They then prepared routers for cyber attacks.
Der Spiegel reporters visited Stellar at its headquarters in Hürth, near Cologne, and presented the documents to Steffen and three of his “tasked” employees. They were able to recognize, among other things, a listing for their central server as well as the company’s mail server, which the GCHQ attackers appear to have hacked.
The document also lays out the intelligence gathered from the spying efforts, including an internal table that shows which Stellar customers are being served by which specific satellite transponders. “Those are business secrets and sensitive information,” said Stellar’s visibly shocked IT chief, Ali Fares, who is himself cited in the document as an employee to be “tasked.”
The Stellar officials expressed alarm when they saw the password for the central server of an important customer. The significance of the theft is immense, Fares said. “This is really disturbing.”
Steffen, after spitting out his four-letter assessment, said he considers the documents to constitute proof that his company’s systems were breached illegally. “The hacked server has always stood behind our company’s own firewall,” he said. “The only way of accessing it is if you first successfully break into our network.” The company in question is no longer a customer with Stellar.
When asked if there are any reasons that would prompt England, a European Union partner country, to take such an aggressive approach to Stellar, Steffen shrugged his shoulders, perplexed. “Our customer traffic doesn’t run across conventional fiber optic lines,” he said. “In the eyes of intelligence services, we are apparently seen as difficult to access.” Still, he said, “that doesn’t give anyone the right to break in.”
“A cyber attack of this nature is a clear criminal offense under German law,” he continued. “I want to know why we were a target and exactly how the attack against us was conducted—if for no other reason than to be able to protect myself and my customers from this happening again.” Steffen wrote a letter to the British ambassador in Berlin asking for an explanation, but says he never received an answer.
Meanwhile, Deutsche Telekom’s security division has conducted a forensic review of important routers in Germany, but has yet to detect anything. Volker Tschersich, who heads the security division, says it’s possible the red dots in Treasure Map can be explained as access to the TAT14 cable, in which Telekom occupies a frequency band in England and the U.S. At the end of last week, the company informed Germany’s Federal Office for Information Security of the findings of Der Speigel‘s reporting.
The classified documents also indicate that other data from Germany contributes to keeping the global treasure map up to date. Of the 13 servers the NSA operates around the world in order to track current data flows on the open Internet, one is located somewhere in Germany.
Like the other servers, this one, which feeds data into the secret NSA network, is “covered” in an inconspicuous “data center.”
_________________________
Email the authors: amm@datenreisen.de, laura.poitras@theintercept.com, marcel_rosenbach@spiegel.de, michael_sontheimer@spiegel.de, christian@grothoff.org
Go to Original – firstlook.org
DISCLAIMER: The statements, views and opinions expressed in pieces republished here are solely those of the authors and do not necessarily represent those of TMS. In accordance with title 17 U.S.C. section 107, this material is distributed without profit to those who have expressed a prior interest in receiving the included information for research and educational purposes. TMS has no affiliation whatsoever with the originator of this article nor is TMS endorsed or sponsored by the originator. “GO TO ORIGINAL” links are provided as a convenience to our readers and allow for verification of authenticity. However, as originating pages are often updated by their originating host sites, the versions posted may not match the versions our readers view when clicking the “GO TO ORIGINAL” links. This site contains copyrighted material the use of which has not always been specifically authorized by the copyright owner. We are making such material available in our efforts to advance understanding of environmental, political, human rights, economic, democracy, scientific, and social justice issues, etc. We believe this constitutes a ‘fair use’ of any such copyrighted material as provided for in section 107 of the US Copyright Law. In accordance with Title 17 U.S.C. Section 107, the material on this site is distributed without profit to those who have expressed a prior interest in receiving the included information for research and educational purposes. For more information go to: http://www.law.cornell.edu/uscode/17/107.shtml. If you wish to use copyrighted material from this site for purposes of your own that go beyond ‘fair use’, you must obtain permission from the copyright owner.
Read more
Click here to go to the current weekly digest or pick another article:
WHISTLEBLOWING - SURVEILLANCE: